En el blog echaremos un vistazo a la vulnerabilidad de Log4Shell y proporcionaremos ejemplos reales de cómo Darktrace detecta y responde a los ataques que intentan aprovechar Log4Shell.
Log4Shell es el ya famoso nombre de CVE-2021-44228, una vulnerabilidad de día cero de gravedad 10 que aprovecha una conocida utilidad de registro de Java conocida como Log4J. Las vulnerabilidades se descubren diariamente y algunas son más graves que otras, pero el hecho de que esta utilidad de código abierto está anidada en casi todo, incluyendo el dron de Mars Ingenuity, hace que esto sea mucho más amenazador. Los detalles y las actualizaciones adicionales sobre Log4Shell todavía están emergiendo en la fecha de la publicación de este blog.
Normalmente, los días cero con el poder de alcanzar estos muchos sistemas no corren riesgos y solo los estados nacionales los utilizan para objetivos u operaciones de alto valor. Este, sin embargo, se descubrió por primera vez que se utilizaba contra los servidores de juegos de Minecraft, compartidos en el chat entre los jugadores.
Aunque se deben tomar todos los pasos para implementar las mitigaciones en la vulnerabilidad Log4Shell, estas pueden tomar tiempo. Como se evidencia aquí, la detección de comportamiento se puede utilizar para buscar señales de actividad post-explotación como exploración, minería de monedas, movimiento lateral y otras actividades.
Darktrace detectó inicialmente la vulnerabilidad de Log4Shell dirigida a uno de los servidores orientados a Internet de nuestros clientes, como verá en detalle a continuación en una investigación de amenazas anonimizadas. Esto se destacó y se informó mediante Cyber AI Analyst, desempacado aquí por nuestro equipo de SOC. Tenga en cuenta que estaba utilizando algoritmos preexistentes sin clasificadores de reentrenamiento ni mecanismos de respuesta de ajuste en reacción a los ciberataques de Log4Shell.
Cómo funciona Log4Shell
La vulnerabilidad funciona al aprovechar la validación incorrecta de entradas por parte de Java Naming and Directory Interface (JNDI, por sus siglas en inglés). Un comando procede de un agente de usuario HTTP, una conexión HTTPS cifrada o incluso un mensaje de sala de chat y JNDI lo envía al sistema de destino en el que se ejecuta. La mayoría de las bibliotecas y aplicaciones tienen controles y protecciones para evitar que esto suceda, pero como se ve aquí, a veces se pierden.
Varios ciberdelincuentes han comenzado a aprovechar la vulnerabilidad en sus ataques, desde mediante campañas indiscriminadas de criptografía y minería hasta ataques dirigidos y más sofisticados.
Ejemplo del mundo real 1: Log4Shell implementado en la fecha de lanzamiento del ID de CVE
Darktrace vio este primer ejemplo el 10 de diciembre, el mismo día en que se publicó el ID de CVE. A menudo vemos vulnerabilidades públicamente documentadas que están siendo armadas en pocos días por ciberdelincuentes. Este ataque afectó a un dispositivo orientado a Internet en la zona desmilitarizada (DMZ) de una organización. Darktrace había clasificado automáticamente el servidor como un dispositivo orientado a Internet en función de su comportamiento.
La organización había implementado Darktrace en la red de la empresa como una de las muchas áreas de cobertura que incluyen la nube, el correo electrónico y SaaS. En esta implementación, Darktrace tenía una buena visibilidad del tráfico DMZ. Antigena no estaba activo en este entorno y Darktrace solo estaba en modo de detección. A pesar de esto, el cliente en cuestión pudo identificar y remediar este incidente en pocas horas tras la alerta inicial. El ataque fue automatizado y tuvo el objetivo de desplegar un criptominero conocido como Kinsing.
En este ataque, el atacante hizo más difícil detectar el ataque mediante el cifrado de la inyección inicial de comandos mediante HTTPS sobre el HTTP más común que se ve habitualmente. A pesar de que este método podía omitir las reglas tradicionales y los sistemas basados en firmas, Darktrace pudo detectar varios comportamientos inusuales segundos después de la conexión inicial.
Detalles del ataque inicial
A través del análisis por pares, Darktrace había aprendido previamente lo que este dispositivo DMZ específico y su grupo de pares hacen normalmente en el entorno. Durante la explotación inicial, Darktrace detectó varias anomalías sutiles que juntas hicieron obvio el ataque.
- 15:45:32 Conexión HTTPS entrante al servidor DMZ desde una dirección IP rusa rara — 45.155.205[.]233;
- 15:45:38 El servidor DMZ realiza una nueva conexión saliente a la misma IP rusa rara mediante dos nuevos agentes de usuario: Agente de usuario Java y "curl" sobre un puerto que es inusual para servir HTTP en comparación con el comportamiento anterior;
- 15:45:39 El servidor DMZ utiliza una conexión HTTP con otro nuevo agente de usuario de cURL ('curl/7.47.0') a la misma IP rusa. El URI contiene información de reconocimiento del servidor DMZ.
Toda esta actividad se detectó no porque Darktrace la hubiera visto antes, sino porque se desviaba fuertemente del “patrón de vida” regular para este y otros servidores similares en esta organización específica.
Este servidor nunca llegó a direcciones IP raras en Internet, sino que utilizó agentes de usuario que nunca antes se habían utilizado, a través de combinaciones de protocolo y puerto que no utiliza habitualmente. Cada anomalía puntual puede haber presentado un comportamiento ligeramente inusual, pero, en conjunto y analizado en el contexto de este dispositivo y entorno en particular, las detecciones cuentan claramente una historia más amplia de un ciberataque en curso.
Darktrace detectó esta actividad con varios modelos, por ejemplo:
- Anomalous Connection / New User Agent to IP Without Hostname
- Anomalous Connection / Callback on Web Facing Device
Descarga de herramientas adicionales y criptominería
Menos de 90 minutos después del ataque inicial, el servidor infectado comenzó a descargar secuencias de comandos y ejecutables malintencionados de una rara IP ucraniana 80.71.158[.]12.
Las siguientes cargas útiles se descargaron posteriormente desde la IP de Ucrania en orden:
- hXXp://80.71.158[.]12//lh.sh
- hXXp://80.71.158[.]12/Expl[REDACTED].class
- hXXp://80.71.158[.]12/kinsing
- hXXp://80.71.158[.]12//libsystem.so
- hXXp://80.71.158[.]12/Expl[REDACTED].class
Sin utilizar inteligencia de amenazas ni detecciones basadas en indicadores estáticos de compromiso (IOC) como IP, nombres de dominio o hash de archivo, Darktrace detectó este siguiente paso en el ataque en tiempo real.
El servidor DMZ en cuestión nunca se había comunicado con esta dirección IP ucraniana en el pasado a través de estos puertos poco comunes. También era muy inusual que este dispositivo y sus pares descargaran secuencias de comandos o archivos ejecutables de este tipo de destino externo y de esta manera. Poco después de estas descargas, el servidor DMZ comenzó la criptominería.
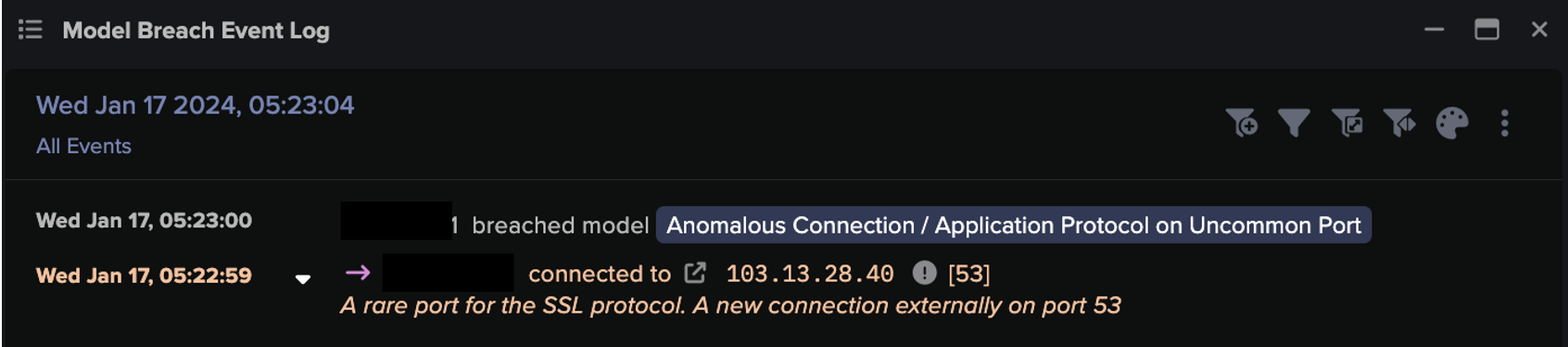
Darktrace detectó esta actividad con varios modelos, por ejemplo:
- Anomalous File / Script from Rare External Location
- Anomalous File / Internet Facing System File Download
- Device / Internet Facing System with High Priority Alert
Detección inmediata de la vulnerabilidad Log4Shell
Además de que Darktrace detectara cada paso individual de este ataque en tiempo real, Darktrace Cyber AI Analyst también hizo surgir el incidente de seguridad general, que contenía una narrativa coherente para el ataque general, como el incidente de mayor prioridad en una semana de incidentes y alertas en Darktrace. Esto significa que este incidente fue el tema más obvio e inmediato destacado a los equipos de seguridad humana a medida que se fue desarrollando. Cyber AI Analyst de Darktrace encontró cada etapa de este incidente y formuló las mismas preguntas que esperaría de sus analistas humanos del SOC. A partir del informe en lenguaje natural generado por Cyber AI Analyst, se presenta (en un formato fácil de entender) un resumen de cada etapa del incidente seguido de los puntos de datos vitales que necesitan los analistas humanos. Cada pestaña significa una parte diferente de esta incidencia y describe los pasos reales que se han tomado durante cada proceso de investigación.
El resultado es que no hay que pasar por alertas de bajo nivel, no hay necesidad de clasificar las detecciones puntuales, no hay que colocar las detecciones en un contexto de incidentes más grande, no hay necesidad de escribir un informe. Todo esto fue completado automáticamente por AI Analyst, ahorrando a los equipos humanos un valioso tiempo.
El siguiente informe de incidencias se creó automáticamente y se puede descargar en formato PDF en varios idiomas.
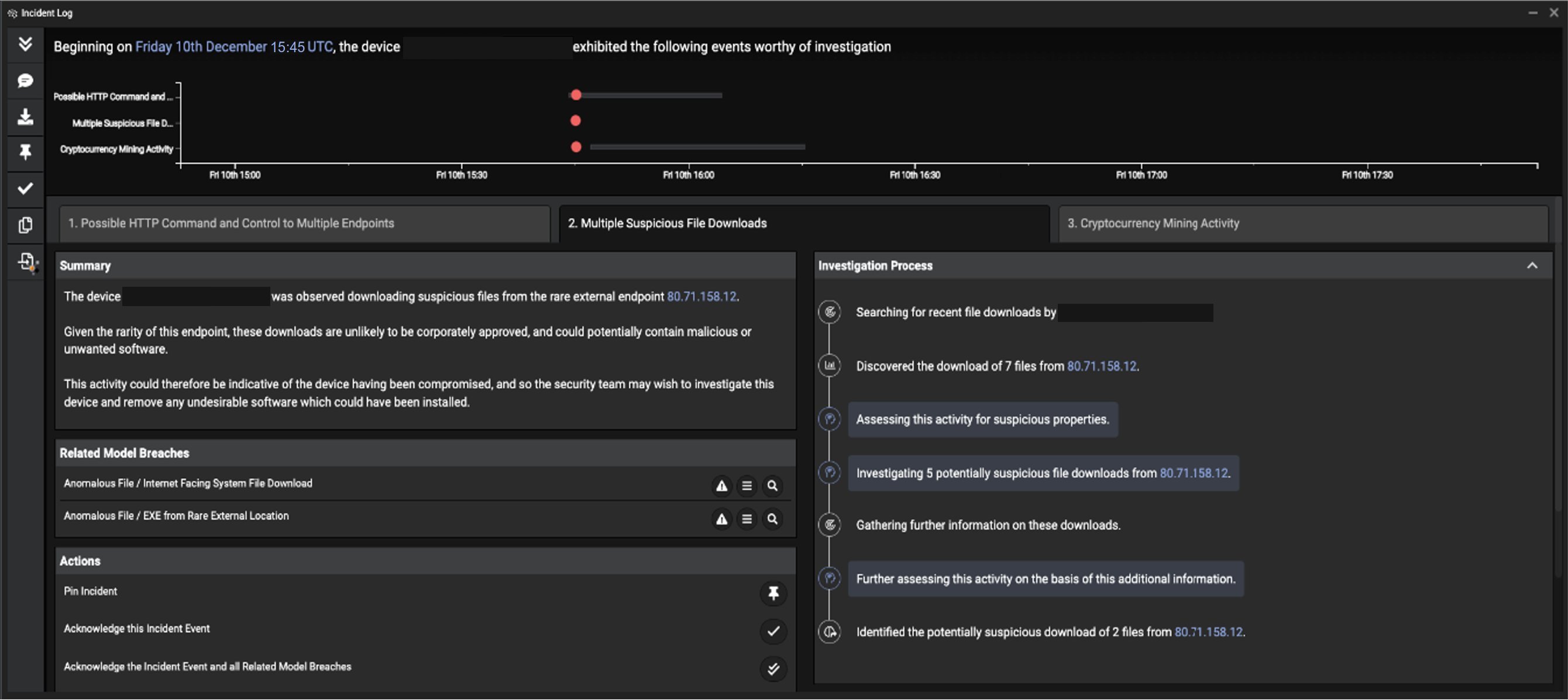
Ilustración 1: Cyber AI Analyst de Darktrace aborda varias etapas del ataque y explica su proceso de investigación
Ejemplo del mundo real 2: Respuesta a un ataque diferente de Log4Shell
El 12 de diciembre, el servidor orientado a Internet de otra organización se vio atacado inicialmente a través de Log4Shell. Si bien los detalles de lo que se vio afectado son diferentes (hay otras IOC involucradas), Darktrace detectó e hizo emerger el ataque de forma similar al primer ejemplo.
Curiosamente, esta organización tenía a Darktrace Antigena en modo autónomo en su servidor, lo que significa que la IA pudo tomar acciones de forma autónoma para responder a los ciberataques. Estas respuestas se pueden entregar a través de una variedad de mecanismos, por ejemplo, interacciones API con firewalls y otras herramientas de seguridad, o respuestas nativas emitidas por Darktrace.
En este ataque, la nada habitual IP externa 164.52.212[.]196 se utilizó para la comunicación de comando y control (C2) y la entrega de malware, utilizando HTTP sobre el puerto 88, lo que era muy inusual para este dispositivo, grupo de pares y organización.
Antigena reaccionó en tiempo real en esta organización, basándose en el contexto específico del ataque, sin ningún ser humano en el medio. Antigena interactuó con el firewall de la empresa en este caso para bloquear cualquier conexión hacia o desde la dirección IP maliciosa (en este caso 164.52.212[.]196) a través del puerto 88 durante 2 horas con la opción de escalar el bloque y la duración si el ataque parecía persistir. Esto se puede ver en la siguiente ilustración:
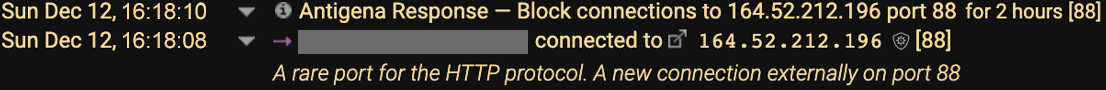
Ilustración 2: La respuesta de Antigena
Aquí viene el truco: gracias a la IA de autoaprendizaje, Darktrace sabe exactamente lo que el servidor orientado a Internet suele hacer y no, incluidos los más mínimos detalles. En base a las diversas anomalías, Darktrace está seguro de que esto representa un gran ciberataque.
Antigena ahora se encarga de aplicar el patrón de vida habitual de este servidor en la DMZ. Esto significa que el servidor puede seguir haciendo lo que normalmente hace, pero todas las acciones altamente anómalas se interrumpen a medida que se producen en tiempo real, como hablar con una rara IP externa a través del puerto 88 que sirve HTTP para descargar ejecutables.
Por supuesto, el ser humano puede cambiar o levantar el bloqueo en cualquier momento dado. Antigena también se puede configurar para que esté en modo de confirmación humana, teniendo a una persona presente a ciertas horas durante el día (por ejemplo, horas de oficina) o en todo momento, dependiendo de las necesidades y requisitos de una organización.
Conclusion
Este blog ilustra otros aspectos de los ciberataques que aprovechan la vulnerabilidad de Log4Shell. También demuestra cómo Darktrace detecta y responde a los ataques de día cero si Darktrace tiene visibilidad de las entidades atacadas.
Si bien Log4Shell domina las noticias de TI y seguridad, en el pasado han surgido vulnerabilidades similares que aparecerán en el futuro. Hemos hablado de nuestro enfoque para detectar y responder a vulnerabilidades similares y ataques cibernéticos en torno, por ejemplo:
- la 'reciente vulnerabilidad Gitlab;
- las vulnerabilidades de ProxyShell Exchange Server cuando todavía estaban a día cero;
- y la vulnerabilidad de Citrix Netscaler
Como siempre, las empresas deben buscar una estrategia de defensa en profundidad que combine controles de seguridad preventivos con mecanismos de detección y respuesta, así como una sólida gestión de parches.
Gracias a Brianna Leddy (Directora de análisis de Darktrace) por sus conocimientos sobre el hallazgo de las amenazas anteriormente citadas.