Es habitual que los atacantes envíen grandes volúmenes de correos maliciosos desde las cuentas de correo electrónico que comprometen. Antes de llevar a cabo esta actividad de envío masivo de correos electrónicos, hay pasos preparatorios predecibles que los atacantes realizan, como el registro de aplicaciones de envío masivo de correos electrónicos y la creación de nuevas reglas de bandeja de entrada. En este blog, proporcionaremos detalles de un ataque observado en febrero de 2022 en el que un actor de la amenaza llevó a cabo un exitoso ataque de correo masivo en una empresa financiera con sede en África.
Resumen del ataque
En febrero de 2022, un atacante intentó infiltrarse en el entorno de correo electrónico de una empresa de servicios financieros con sede en África. A principios de febrero, el atacante probablemente consiguió introducirse en el entorno de correo electrónico de la empresa engañando a un usuario interno para que introdujera las credenciales de su cuenta de correo electrónico corporativa en una página de phishing. A lo largo de la semana siguiente, el atacante utilizó las credenciales de la cuenta comprometida para llevar a cabo diversas actividades, como el registro de una aplicación de correo masivo y la creación de una nueva regla de bandeja de entrada.
Después de dar estos pasos preparatorios, el atacante pasó a enviar grandes volúmenes de correos electrónicos de phishing desde la cuenta de correo electrónico del usuario interno. El atacante obtuvo entonces las credenciales de varias cuentas corporativas internas más. Utilizó las credenciales de una de estas cuentas para llevar a cabo pasos preparatorios similares (registrar una aplicación de correo masivo y crear una nueva regla de bandeja de entrada). Tras realizar estos pasos, el atacante volvió a enviar grandes volúmenes de correos electrónicos de phishing desde la cuenta. En este punto, el cliente solicitó la asistencia del SOC de Darktracepara ayudar a la investigación, y la intrusión fue consecuentemente contenida por la compañía.
Dado que el atacante llevó a cabo sus actividades utilizando una VPN y un servicio en la nube de Amazon, los puntos finales desde los que se realizaron las actividades no sirvieron como indicadores especialmente útiles de un ataque. Sin embargo, antes de enviar los correos electrónicos de phishing desde las cuentas de los usuarios internos, el atacante llevó a cabo otras actividades preparatorias predecibles. Uno de los principales objetivos de este blog es destacar que estos comportamientos sirven como valiosos indicios de preparación para una actividad de envío masivo de correos electrónicos.
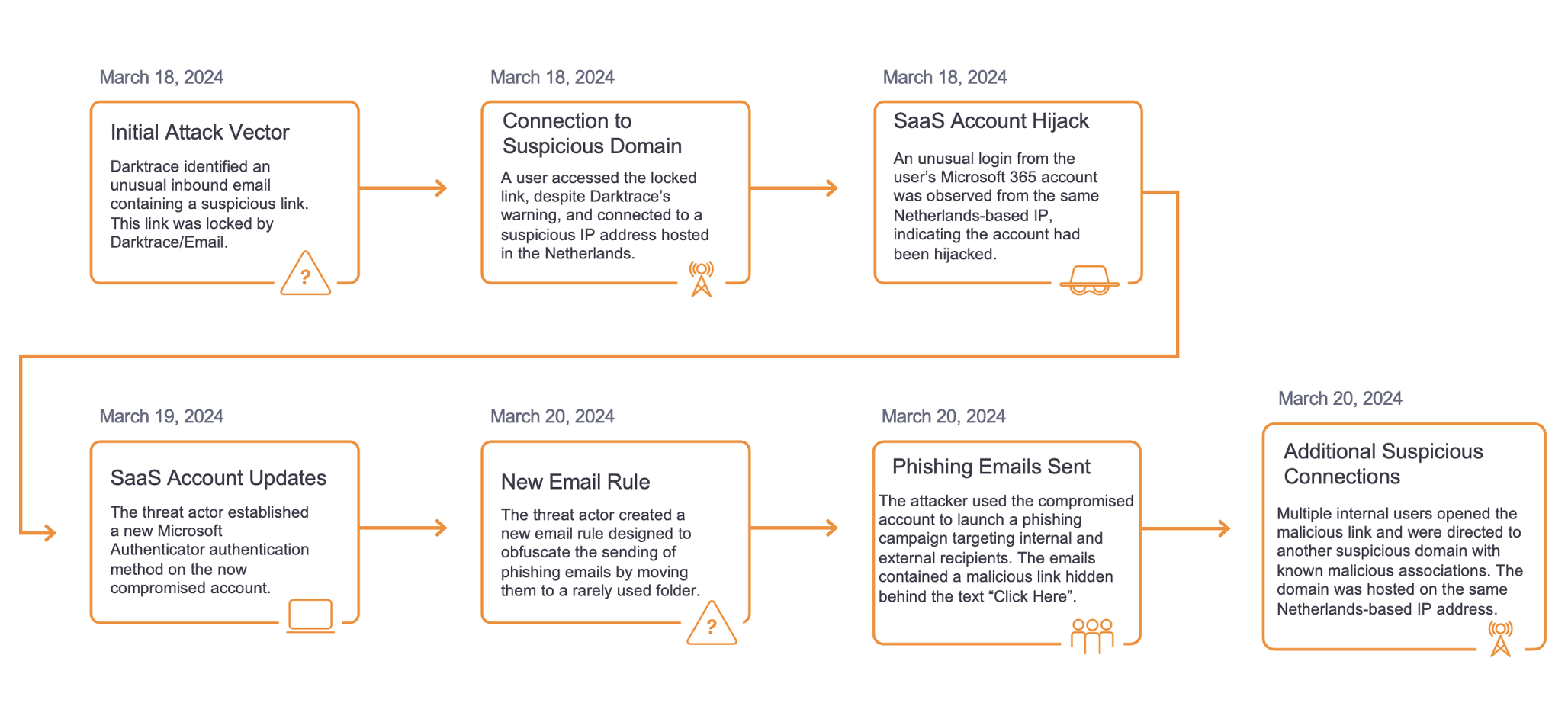
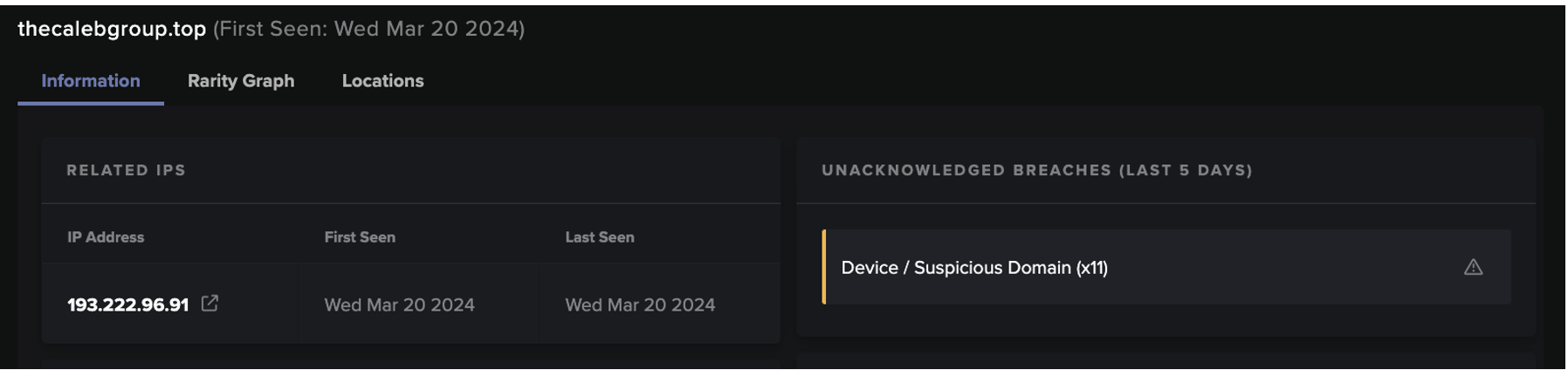
Cronología del ataque

Figura 1: Cronología de la intrusión
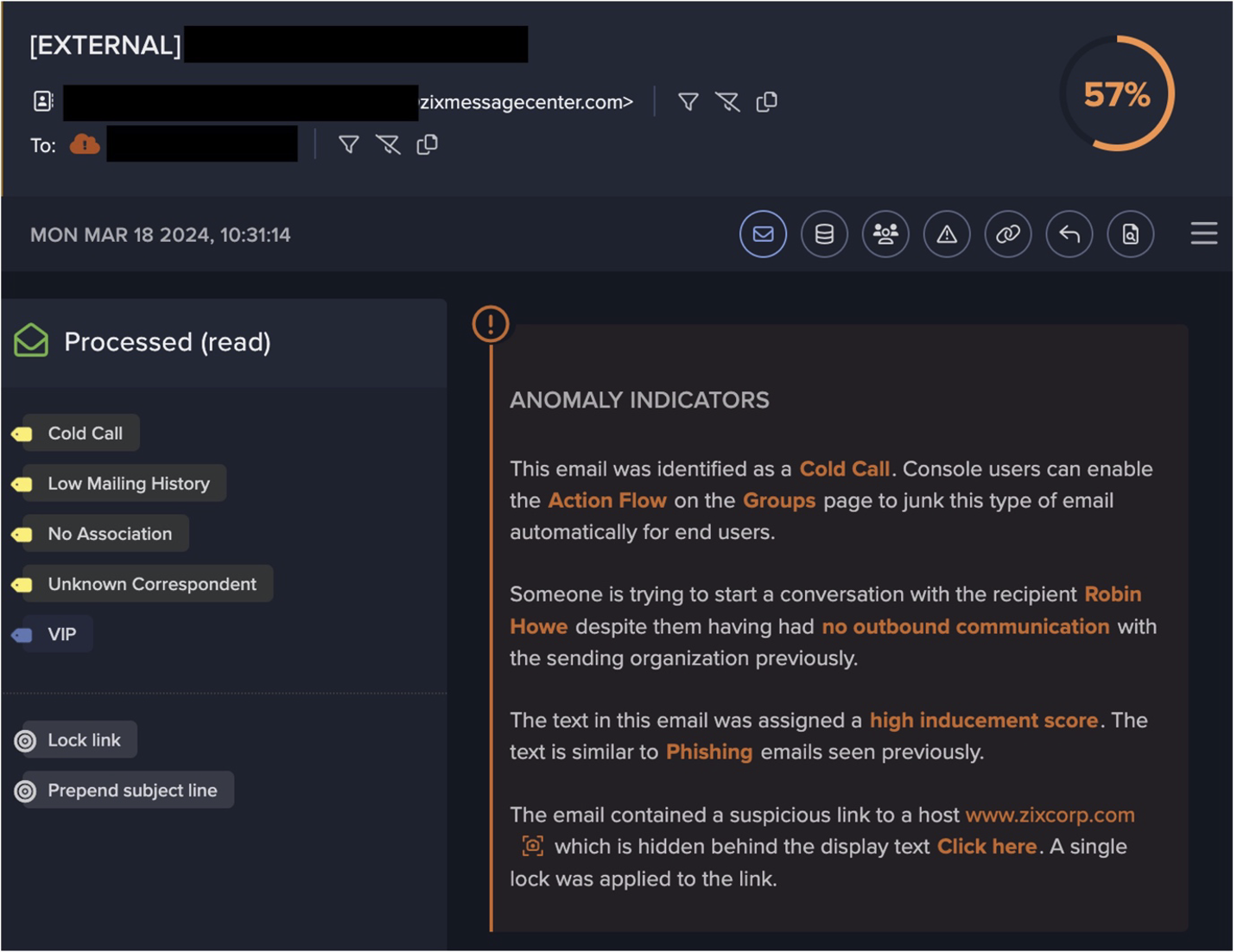
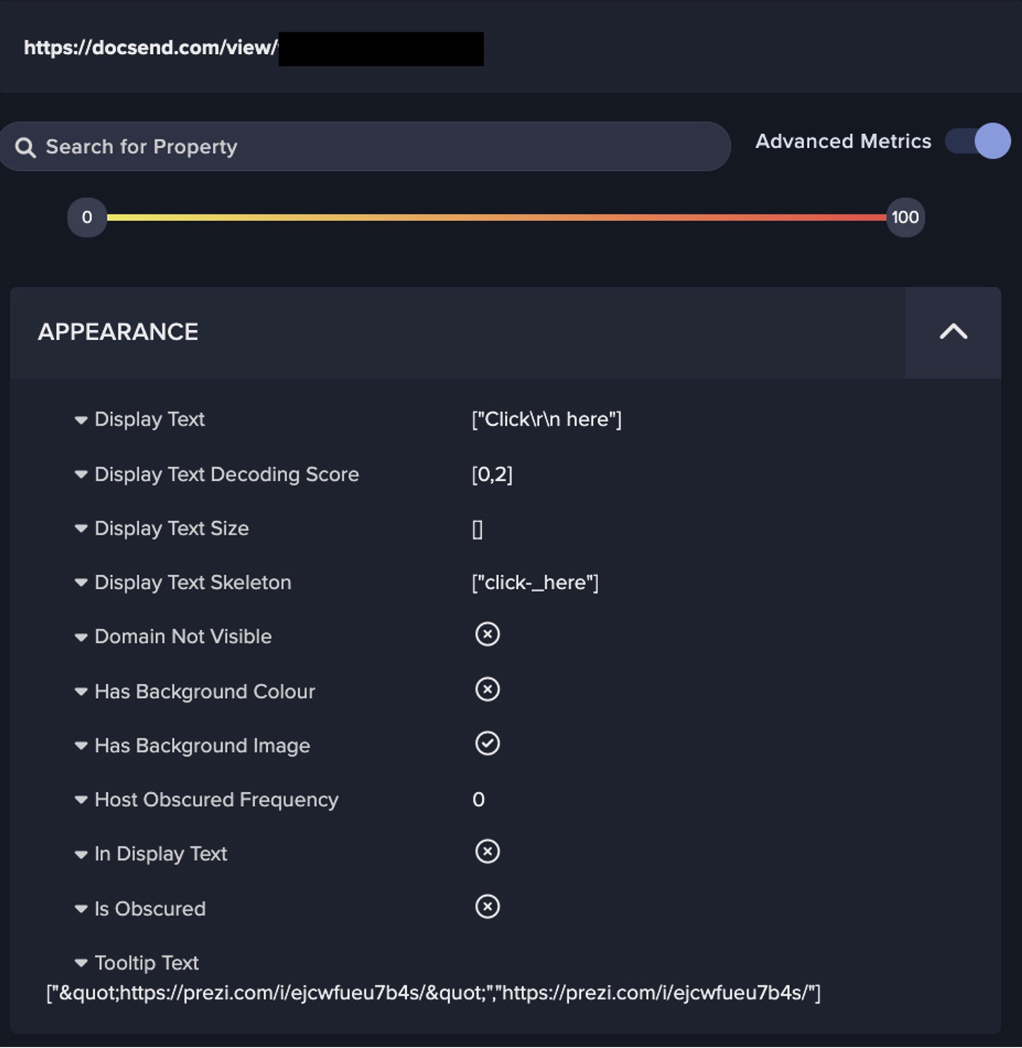
El 3 de febrero, el atacante envió un correo electrónico de phishing a la cuenta corporativa de un empleado. El correo electrónico se envió desde la cuenta corporativa de un empleado de una empresa con vínculos comerciales con la empresa víctima. Es probable que el atacante haya comprometido esta cuenta antes de enviar el correo electrónico de phishing desde ella. El correo electrónico de phishing en cuestión decía ser un recordatorio de pago atrasado. Dentro del correo electrónico, había un enlace oculto tras el texto "ver factura". El nombre de host de la URL del enlace de phishing era un subdominio de questionpro[.]eu, una plataforma de encuestas en línea. La página a la que hacía referencia la URL era una página de inicio de sesión falsa de Microsoft Outlook.

Figura 2: Destino del enlace de phishing dentro del correo electrónico enviado por el atacante
Antigena Email, la solución de seguridad de correo electrónico de Darktrace, identificó la estructura lingüística altamente inusual del correo electrónico, dada su comprensión de lo "normal" para ese remitente. Esto se reflejó en una puntuación de desplazamiento de inducción de 100. Sin embargo, en este caso, la URL original del enlace de phishing fue reescrita por el servicio de protección de URL de Mimecast de forma que la URL completa era imposible de extraer. En consecuencia, Antigena Email no sabía cuál era la URL original del enlace. Como el enlace fue reescrito por el servicio de protección de URL de Mimecast, el destinatario del correo electrónico habrá recibido una notificación de advertencia en su navegador al hacer clic en el enlace. Parece que el destinatario ignoró la advertencia y, en consecuencia, divulgó las credenciales de su cuenta de correo electrónico al atacante.
Para que Antigena Email retenga un correo electrónico del buzón de un usuario, debe juzgar con un alto grado de confianza que el correo electrónico es malicioso. En los casos en los que el correo electrónico no contiene archivos adjuntos o enlaces sospechosos, es difícil que Antigena Email obtenga esos altos grados de confianza, a menos que el correo electrónico muestre claros indicadores maliciosos independientes de la carga útil, como indicadores de suplantación de identidad o indicadores de extorsión. En este caso, el correo electrónico, visto por Antigena Email, no contenía ningún enlace o adjunto sospechoso (ya que Mimecast había reescrito el enlace sospechoso) y el correo electrónico no contenía ningún indicador de suplantación o extorsión.

Figura 3: La elevada puntuación de cambio de inducción del correo electrónico pone de manifiesto que el contenido lingüístico y la estructura del correo electrónico eran inusuales para el remitente del mismo
Poco después de recibir el correo electrónico, se observó que el dispositivo corporativo del usuario interno realizaba conexiones SSL al phishing questionpro[.]eu endpoint. Es probable que el usuario divulgara las credenciales de su cuenta de correo electrónico durante estas conexiones.

Figura 4: La captura de pantalla anterior -obtenida de Advanced Search- muestra las conexiones realizadas por el dispositivo del propietario de la cuenta el 3 de febrero
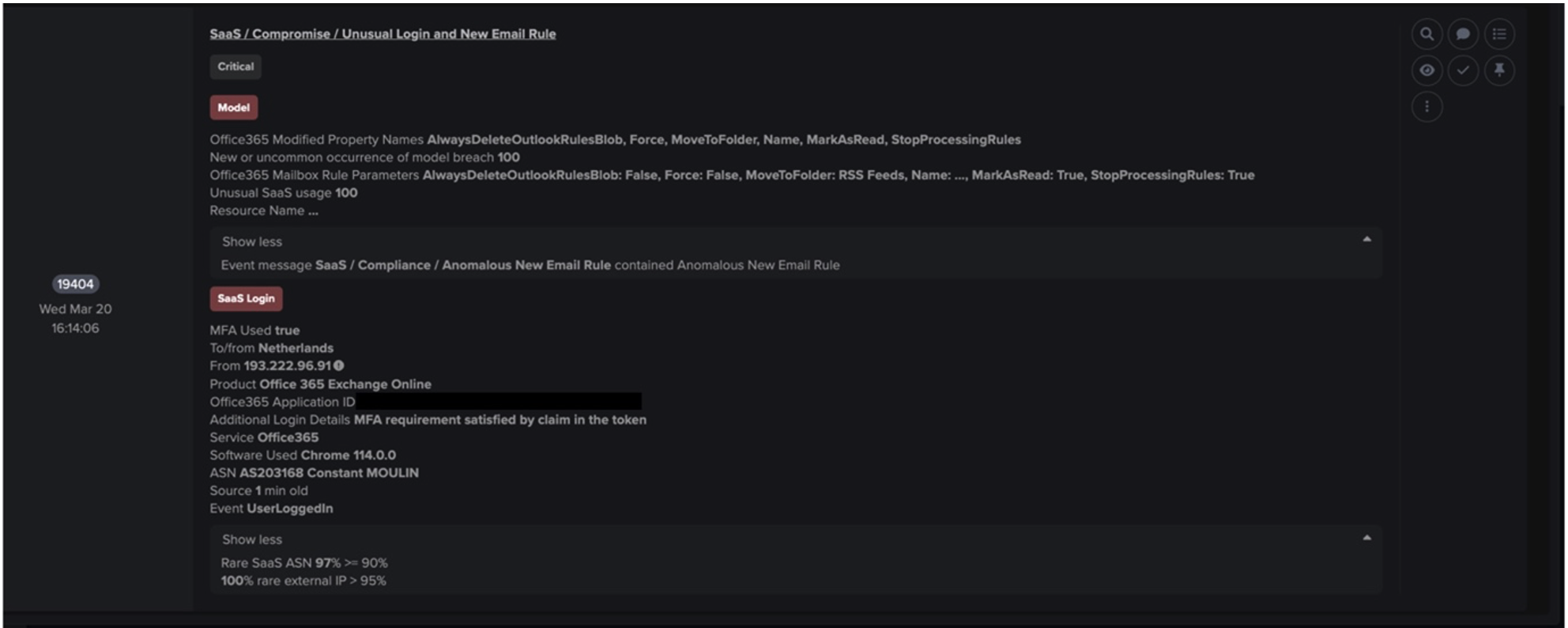
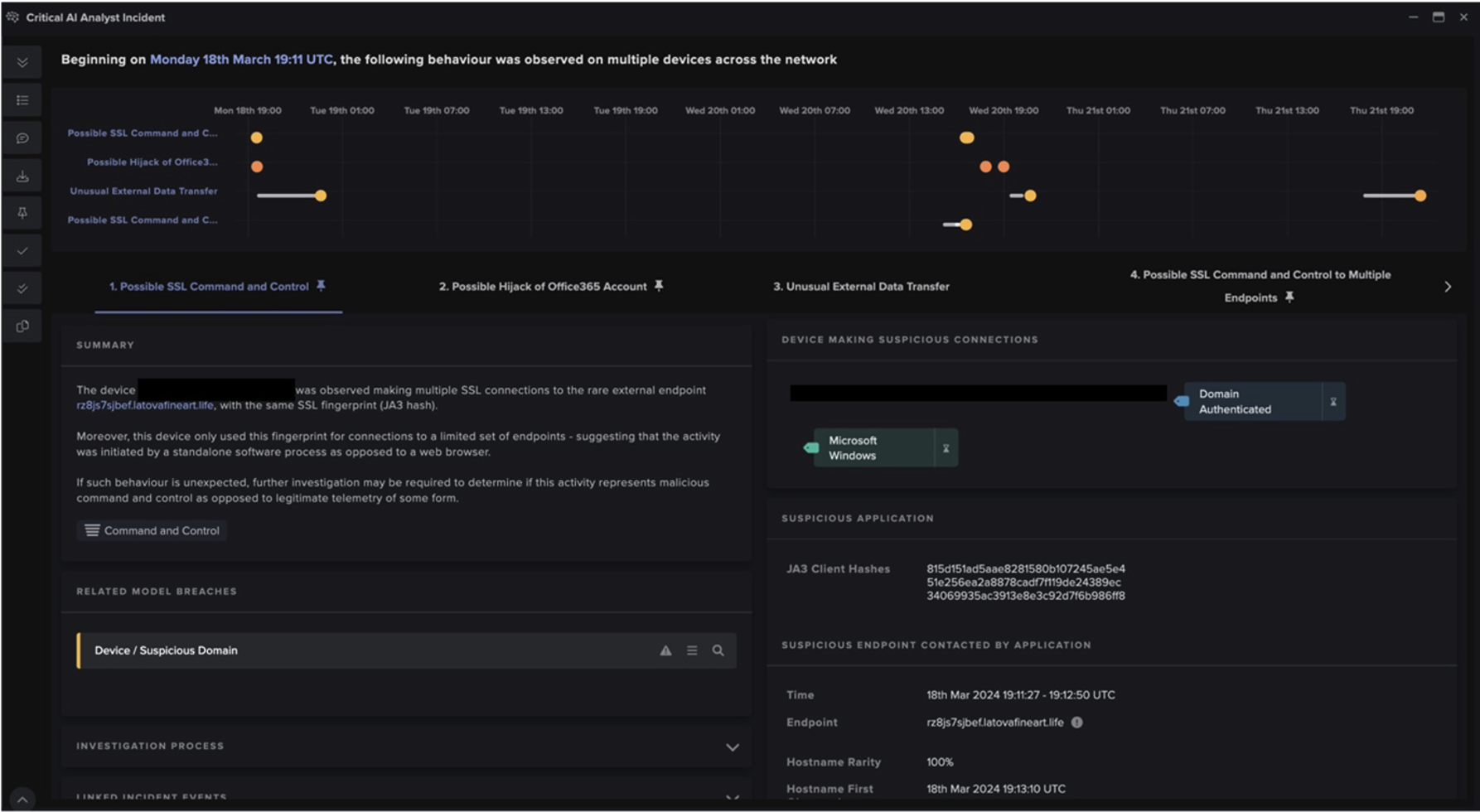
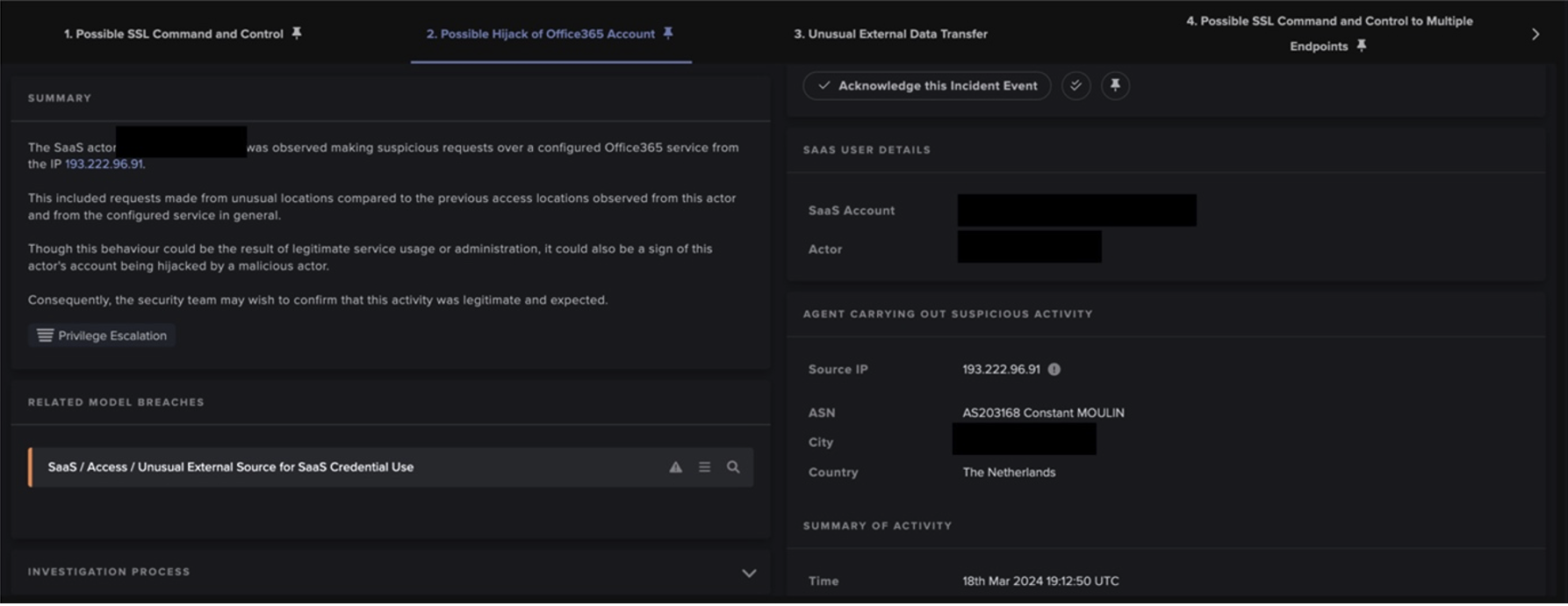
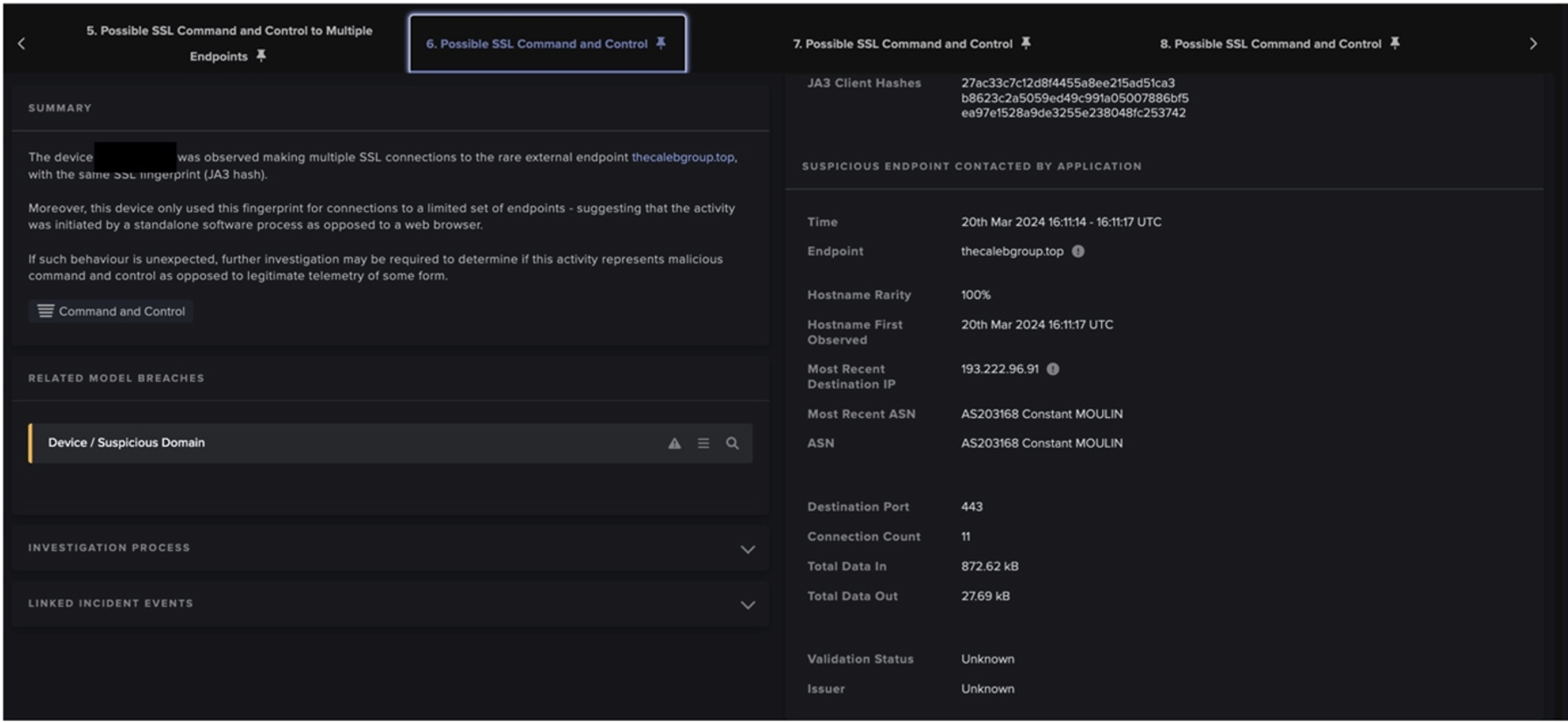
Between February 3 and February 7, the attacker logged into the user’s email account several times. Since these logins were carried out using a common VPN service, they were not identified as particularly unusual by Darktrace. However, during their login sessions, the attacker exhibited behavior which was highly unusual for the email account’s owner. The attacker was observed creating an inbox rule called “ _ ” on the user’s email account,[1] as well as registering and granting permissions to a mass-mailing application called Newsletter Software SuperMailer. These steps were taken by the attacker in preparation for their subsequent mass-mailing activity.
On February 7, the attacker sent out phishing emails from the user’s account. The emails were sent to hundreds of internal and external mailboxes. The email claimed to be an overdue payment reminder and it contained a questionpro[.]eu link hidden behind the display text “view invoice”. It is likely that the inbox rule created by the attacker caused all responses to this phishing email to be deleted. Attackers regularly create inbox rules on the email accounts which they compromise to ensure that responses to the malicious emails which they distribute are hidden from the accounts’ owners.[2]
Dado que Antigena Email no tiene visibilidad de los correos electrónicos de interno a interno, el correo electrónico de phishing se entregó completamente armado a cientos de buzones internos. El 7 de febrero, después de que se enviara el correo electrónico de phishing desde la cuenta interna comprometida, se observaron más de veinte dispositivos internos que realizaban conexiones SSL a la correspondiente questionpro[.]eu endpoint, lo que indica que muchos usuarios internos habían hecho clic en el enlace de phishing y posiblemente habían revelado las credenciales de su cuenta al atacante.

Figura 5: La captura de pantalla anterior -obtenida de Advanced Search- muestra el gran volumen de conexiones realizadas por dispositivos internos al phishing endpoint
Durante los cinco días siguientes, se observó al atacante iniciar sesión en las cuentas de correo electrónico corporativo de al menos seis usuarios internos. Estos inicios de sesión se llevaron a cabo desde los mismos puntos finales de la VPN que los inicios de sesión originales del atacante. El 11 de febrero, el atacante fue observado creando una regla de bandeja de entrada llamada " , " en una de estas cuentas. Poco después, el atacante procedió a registrar y conceder permisos a la misma aplicación de correo masivo, Newsletter Software SuperMailer. Al igual que en el caso de la otra cuenta, el atacante realizó estos pasos como preparación para su posterior actividad de envío masivo de mensajes.

Figura 6: La captura de pantalla anterior -obtenida de Advanced Search- resume todas las acciones relacionadas con la aplicación de correo masivo que realizó el atacante (las cuentas han sido redactadas)
El 11 de febrero, poco después de las 08:30 (UTC), el atacante distribuyó ampliamente un correo electrónico de phishing desde la cuenta de este segundo usuario. El correo electrónico de phishing se distribuyó a cientos de buzones internos y externos. A diferencia de los otros correos electrónicos de phishing utilizados por el atacante, este decía ser una notificación de orden de compra, y contenía un archivo HTML llamado PurchaseOrder.html. Dentro de este archivo, había un enlace a una página sospechosa en el sitio de noticias de relaciones públicas (PR), everything-pr[.]com. Después de que se enviara el correo electrónico de phishing desde la cuenta interna comprometida, se observaron más de veinte dispositivos internos que realizaban conexiones SSL a la página everything-pr[.]com correspondiente endpoint, lo que indicaba que muchos usuarios internos habían abierto el archivo adjunto malicioso.

Figura 7: La captura de pantalla anterior -obtenida de Advanced Search- muestra las conexiones realizadas por los dispositivos internos a la dirección endpoint a la que se hace referencia en el archivo adjunto malicioso
El 11 de febrero, el cliente envió una solicitud de Ask the Expert (ATE) al equipo del SOC de Darktrace. La orientación proporcionada por el SOC ayudó al equipo de seguridad a contener la intrusión. El atacante consiguió mantener su presencia en el entorno de correo electrónico de la organización durante ocho días. Durante estos ocho días, el atacante envió grandes volúmenes de correos electrónicos de phishing desde dos cuentas corporativas. Antes de enviar estos correos electrónicos de phishing, el atacante llevó a cabo acciones preparatorias predecibles. Estas acciones incluían el registro de una aplicación de correo masivo en Azure AD y la creación de una regla de bandeja de entrada.
Recomendaciones de Darktrace
Hay muchos puntos de aprendizaje para esta intrusión en particular. En primer lugar, es importante estar atento a los signos de preparación para la actividad de envío masivo de correos electrónicos maliciosos. Después de que un atacante comprometa una cuenta de correo electrónico, hay varias acciones que probablemente realizará antes de enviar grandes volúmenes de correos electrónicos maliciosos. Por ejemplo, pueden crear una regla de bandeja de entrada en la cuenta, y pueden registrar una aplicación de envío masivo de correos electrónicos con Azure AD. Los modelos Darktrace SaaS / Compliance / New Email Rule y SaaS / Admin / OAuth Permission Grant están diseñados para detectar estos comportamientos.
En segundo lugar, en los casos en los que un atacante consigue enviar correos electrónicos de phishing desde una cuenta corporativa interna, se aconseja que los clientes hagan uso de la búsqueda avanzada de Darktracepara identificar a los usuarios que puedan haber divulgado las credenciales de la cuenta al atacante. El correo electrónico de phishing enviado desde la cuenta comprometida probablemente contendrá un enlace sospechoso. Una vez identificado el nombre de host del enlace, es posible pedir a la Búsqueda Avanzada que muestre todas las conexiones HTTP o SSL al host en cuestión. Si el nombre del host es www.example.com, puede hacer que la Búsqueda Avanzada muestre todas las conexiones SSL al host utilizando la consulta de Búsqueda Avanzada, @fields.server_name: "www.example.com", y puede hacer que la Búsqueda Avanzada muestre todas las conexiones HTTP al host utilizando la consulta, @fields.host: "www.example.com".
Third, it is advised that customers make use of Darktrace’s ‘watched domains’ feature[3] in cases where an attacker succeeds in sending out malicious emails from the accounts they compromise. If a hostname is added to the watched domains list, then a model named Compromise / Watched Domain will breach whenever an internal device is observed connecting to it. If Antigena Network is configured, then observed attempts to connect to the relevant host will be blocked if the hostname is added to the watched domains list with the ‘flag for Antigena’ toggle switched on. If an attacker succeeds in sending out a malicious email from an internal, corporate account, it is advised that customers add hostnames of phishing links within the email to the watched domains list and enable the Antigena flag. Doing so will cause Darktrace to identify and thwart any attempts to connect to the relevant phishing endpoints.
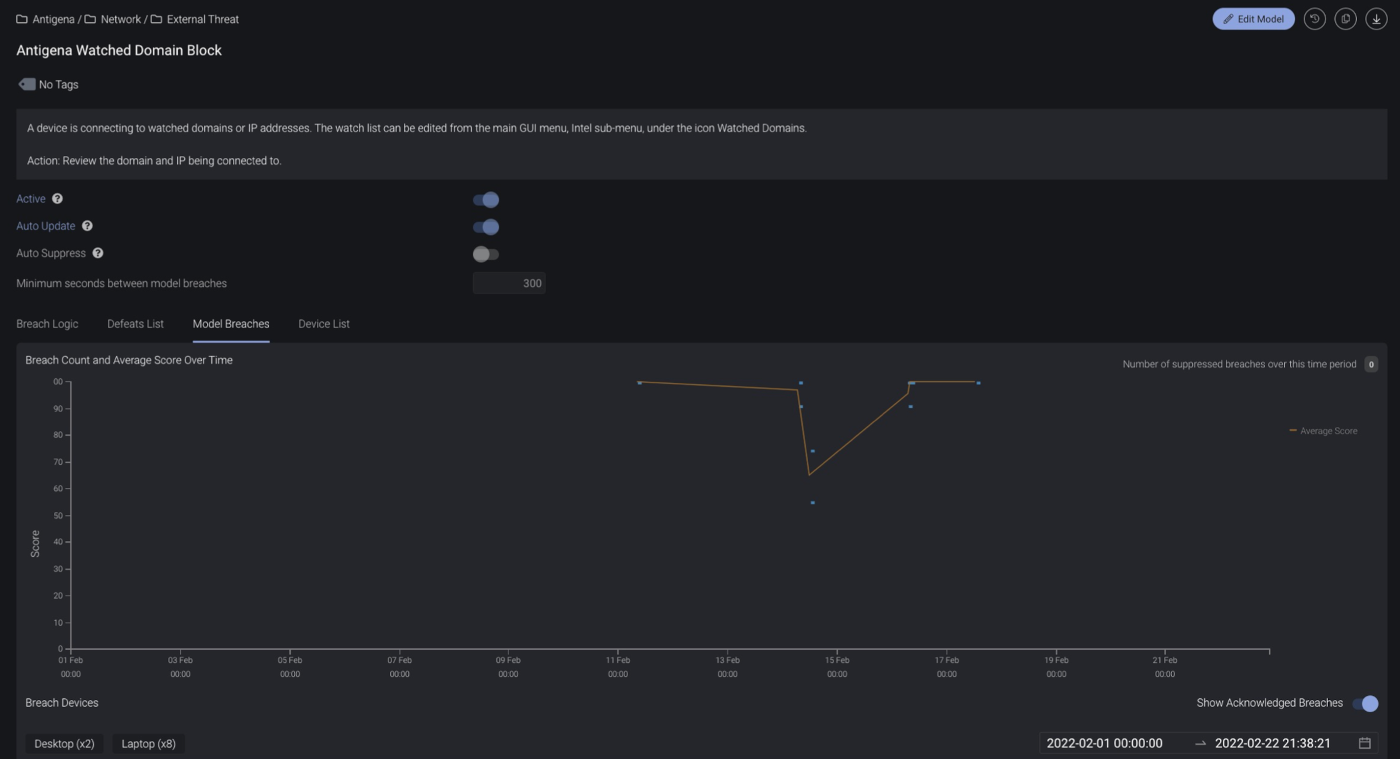
Figura 8: La captura de pantalla anterior -obtenida del Editor de Modelos- muestra que Antigena Network impidió que diez dispositivos internos se conectaran a puntos finales de phishing después de que los nombres de host de phishing pertinentes se añadieran a la lista de dominios vigilados el 11 de febrero
For Darktrace customers who want to find out more about phishing detection, refer here for an exclusive supplement to this blog.
Técnicas ATT&CK de MITRE observadas




Gracias a Paul Jennings por sus contribuciones.
Notas a pie de página
1. https://docs.microsoft.com/en-us/powershell/module/exchange/new-inboxrule?view=exchange-ps
2. https://www.fireeye.com/current-threats/threat-intelligence-reports/rpt-fin4.html
3. https://customerportal.darktrace.com/product-guides/main/watched-domains